The Flare-On Challenge
1 - DrillBabyDrill
题目是python打包的exe,并给了源码,直接看py文件
找到生成flag的函数
1
2
3
4
5
6
7
| def GenerateFlagText(sum):
key = sum >> 8
encoded = "\xd0\xc7\xdf\xdb\xd4\xd0\xd4\xdc\xe3\xdb\xd1\xcd\x9f\xb5\xa7\xa7\xa0\xac\xa3\xb4\x88\xaf\xa6\xaa\xbe\xa8\xe3\xa0\xbe\xff\xb1\xbc\xb9"
plaintext = []
for i in range(0, len(encoded)):
plaintext.append(chr(ord(encoded[i]) ^ (key+i)))
return ''.join(plaintext)
|
sum是未知量,其实可以直接爆破
1
2
3
4
5
6
7
| encoded = b"\xd0\xc7\xdf\xdb\xd4\xd0\xd4\xdc\xe3\xdb\xd1\xcd\x9f\xb5\xa7\xa7\xa0\xac\xa3\xb4\x88\xaf\xa6\xaa\xbe\xa8\xe3\xa0\xbe\xff\xb1\xbc\xb9"
for key in range(2000):
pt = ''.join(chr(encoded[i] ^ (key+i)) for i in range(len(encoded)))
if "flare" in pt.lower():
print(key, pt)
break
|
drilling_for_teddies@flare-on.com
2 - project_chimera
附件是一个py文件
- 读取 encrypted_sequencer_data
↓
- zlib.decompress
↓
得到 marshal 序列化的 code object
↓
- marshal.loads
↓
得到 Python code object
↓
- exec
↓
执行真正逻辑
所以要把 sequencer_code 反编译出来
下面这个脚本跑出源码
1
2
3
4
5
6
7
8
9
10
| import zlib
import marshal
import dis
encrypted_sequencer_data = b'...'
data = zlib.decompress(encrypted_sequencer_data)
code = marshal.loads(data)
dis.dis(code)
|
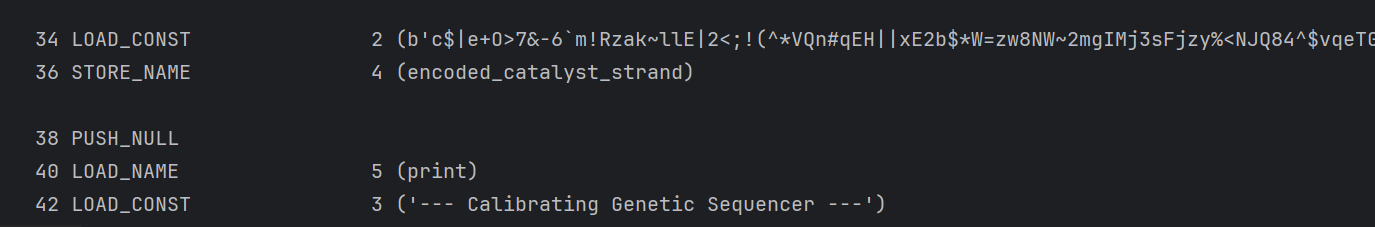
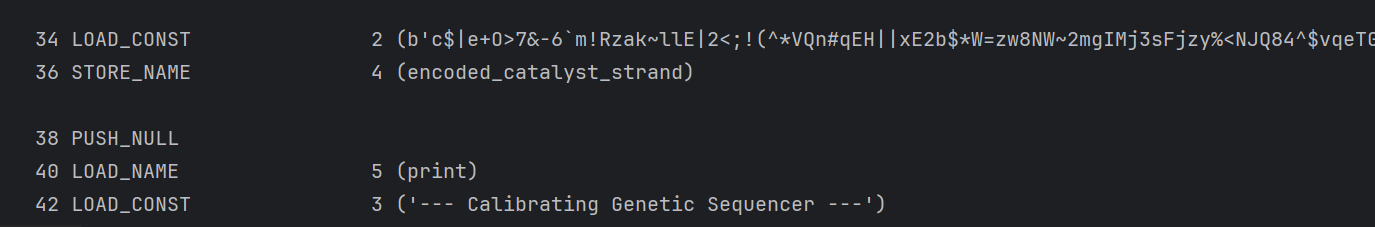
发现了一段base85编码,还有一层编码,真正的程序逻辑在 catalyst_code_object 里
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| import dis
encoded_catalyst_strand = b'...'
compressed_catalyst = base64.b85decode(encoded_catalyst_strand)
marshalled_genetic_code = zlib.decompress(compressed_catalyst)
catalyst_code_object = marshal.loads(marshalled_genetic_code)
print("=== Disassembled Bytecode ===")
dis.dis(catalyst_code_object)
|
得到字节码,gpt还原成python
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
| import os
from arc4 import ARC4
async def activate_catalyst():
LEAD_RESEARCHER_SIGNATURE = b'm\x1b@I\x1dAoe@\x07ZF[BL\rN\n\x0cS'
ENCRYPTED_CHIMERA_FORMULA = b'r2b-\r\x9e\xf2\x1fp\x185\x82\xcf\xfc\x90\x14\xf1O\xad#]\xf3\xe2\xc0L\xd0\xc1e\x0c\xea\xec\xae\x11b\xa7\x8c\xaa!\xa1\x9d\xc2\x90'
print("--- Catalyst Serum Injected ---")
print("Verifying Lead Researcher's credentials via biometric scan...")
current_user = os.getlogin().encode()
user_signature = bytes(
c ^ (i + 42)
for i, c in enumerate(current_user)
)
if user_signature == LEAD_RESEARCHER_SIGNATURE:
print("AUTHENTICATION SUCCESS")
arc4_decipher = ARC4(current_user)
decrypted_formula = arc4_decipher.decrypt(
ENCRYPTED_CHIMERA_FORMULA
).decode()
print("I am alive! The secret formula is:")
print(decrypted_formula)
else:
print("AUTHENTICATION FAILED")
|
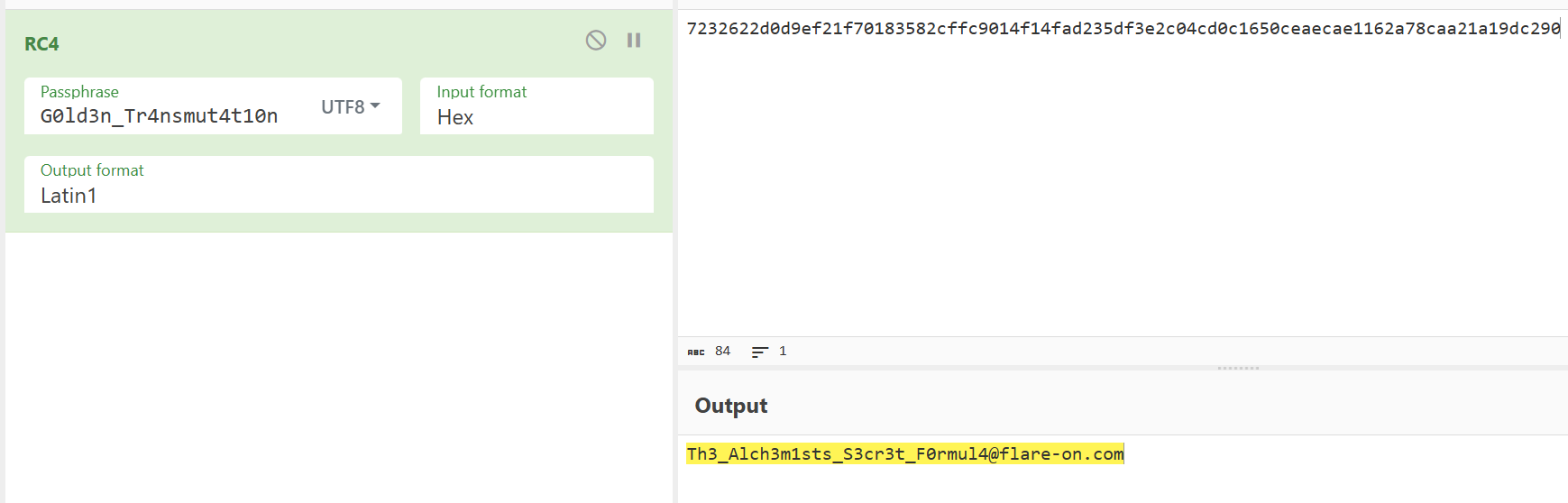
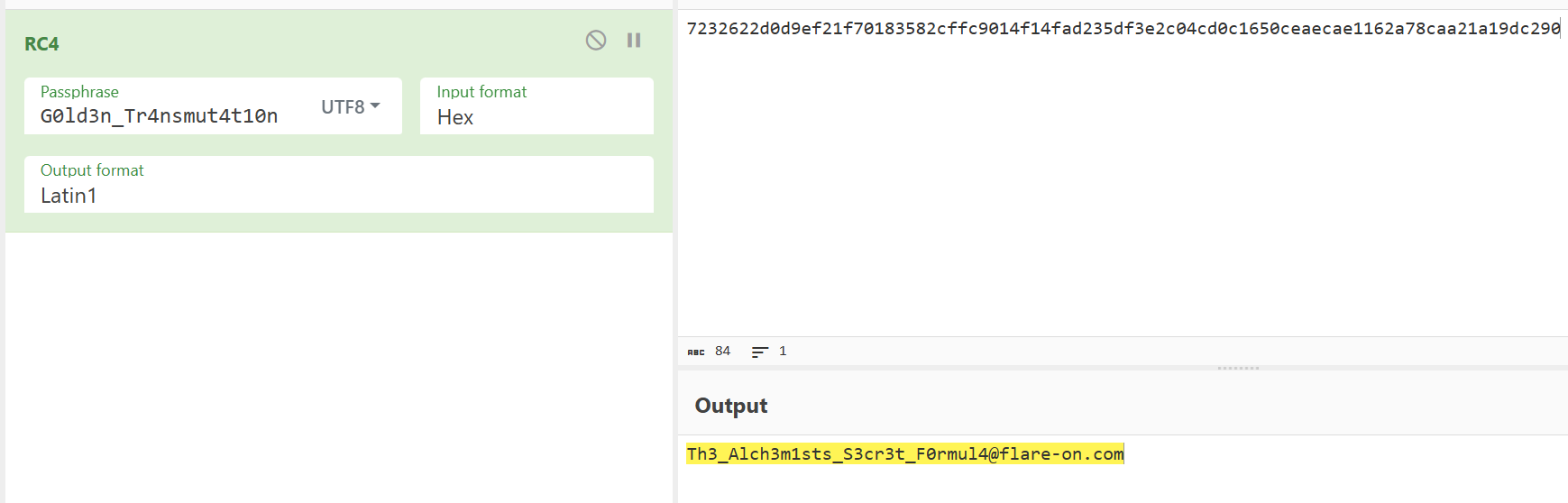
解出用户名
1
2
3
4
5
6
7
8
| sig = b'm\x1b@I\x1dAoe@\x07ZF[BL\rN\n\x0cS'
username = bytes(
sig[i] ^ (i + 42)
for i in range(len(sig))
)
print(username)
|
G0ld3n_Tr4nsmut4t10n
将ENCRYPTED_CHIMERA_FORMULA转为16进制rc4解密
3 - pretty_devilish_file
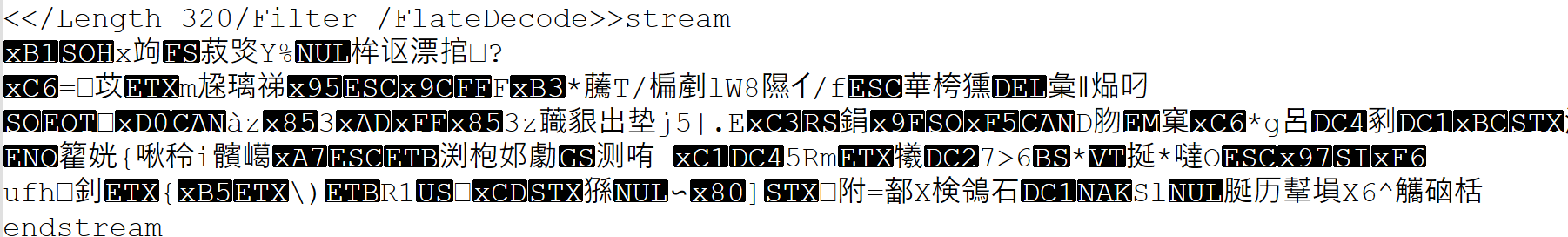
附件是一个pdf文件
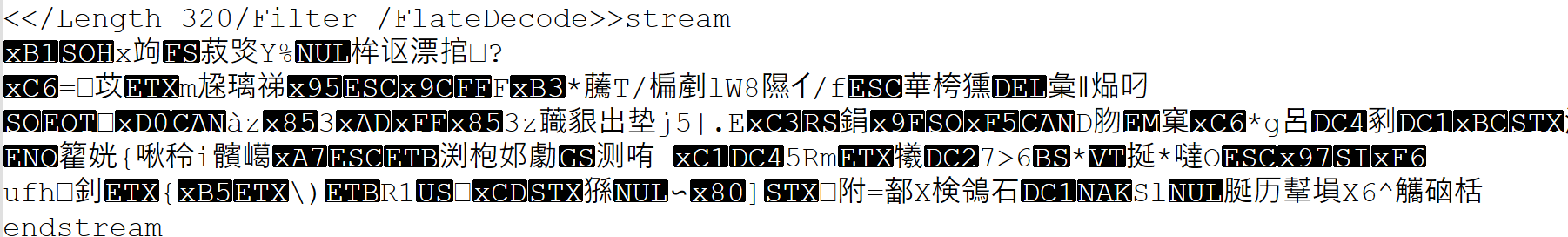
发现一串可疑的字符大小为320字节
打开这个pdf文件,只有chrome浏览器打开是有字的
说明那个字符串是一段代码
看这个The Flare-On Challenge #12 (2025) WriteUp | 棱晶の小窝